Entra ID Application Admin Consent
The Xplicit Trust Network Access application in Entra ID requires admin consent. If you did not grant admin consent during the sign-up process by checking "Consent on behalf of your organization", or if the required permissions have changed and consent has to be granted again, this can be done in the XplicitTrust tenant settings.
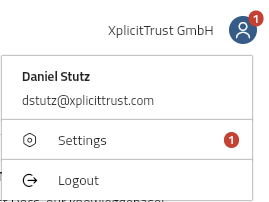
When admin consent has to be granted, a notification is shown in the user menu in the upper right corner of the XplicitTrust Admin Console.
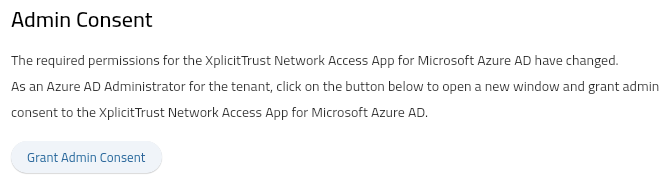
Grant Admin Consent
To grant admin consent
- navigate to the settings page using the user menu in the upper right corner
- click on Grant Admin Consent
- click "Accept" in the Microsoft permissions dialog
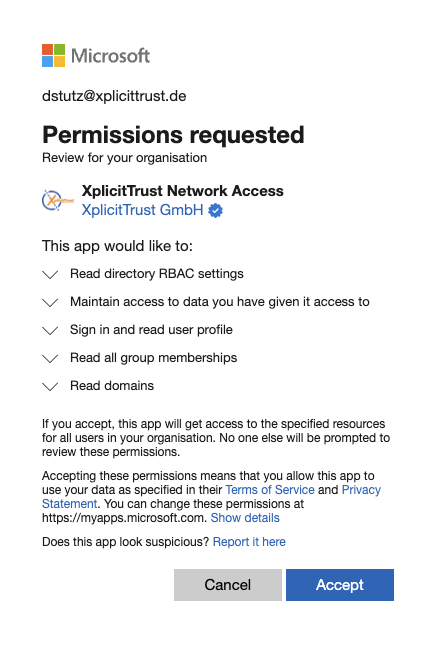
Required Permissions
| Permission | Description | Reason |
|---|---|---|
Sign in and read user profile |
Allows users to sign-in to the app, and allows the app to read the profile of signed-in users. It also allows the app to read basic company information of signed-in users. | To authenticate users against MS Entra ID and read the email, name and group memberships. |
Maintain access to data you have given it access to |
Allows the app to see and update the data you gave it access to, even when users are not currently using the app. This does not give the app any additional permissions. | To get a refresh token from MS Entra ID, that is used for both, the XplicitTrust Network Access Agent and the Admin Console. |
Read directory RBAC settings |
Allows the app to read the role-based access control (RBAC) settings for your company's directory, on behalf of the signed-in user. This includes reading directory role templates, directory roles and memberships. | To allow users with one of the roles Global Administrator, Application Administrator, or Cloud Application Administrator to sign-in to the Admin Console without having to configure Application Roles in MS Entra ID. |
Read all group memberships |
Allows the app to read memberships and basic group properties for all groups without a signed-in user. | Required by the User Groups Import feature, that allows to import groups from MS Entra ID to be used in XplicitTrust Policies. |
Read domains |
Allows the app to read all domain properties without a signed-in user. | To verify domains that are linked to the XplicitTrust Tenant are under the administrative control of the organization. |
To learn more about the required permissions please refer to the Microsoft Graph permissions reference